Netscaler Management and Analytics System (NMAS) is a great tool for managing your Netscaler estate and gaining insight into the traffic flows. In saying that, it doesn’t capture traffic from clients who are connecting to a DNS Load Balanced virtual server, and this is a requirement I recently came across. To capture this traffic, we need to enable syslogs with some minor tweaks. In this case I utilised the built-in syslog server on NMAS, but you could also use the one on the Netscaler itself or a third party solution.
- Netscaler: 12.0 56.20.nc
- Netscaler MAS: 12.0 56.20
1. Enable syslog on the Netscaler
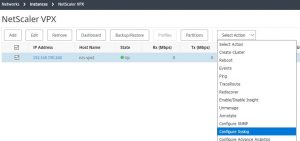
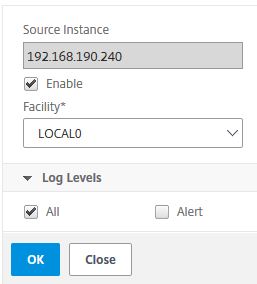
I did this configuration piece from NMAS, but it can be done on the Netscaler itself too. In NMAS, select your Netscaler instance and click on ‘Configure Syslog’. Tick the ‘Enable’ checkbox and select the logging levels you would like to capture. As this is a lab, I selected ‘All’ but in reality you would probably want to turn off ‘Debug’. To capture DNS query traffic, ‘Informational’ must be selected.
Once done, a syslog server and a policy will have been added to the selected Netscaler instance.
2. Configure syslog to capture DNS traffic
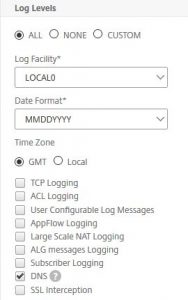
By default, the syslog server created above will not capture DNS traffic. To enable this, edit the syslog server on the Netscaler itself (System / Auditing / Syslog / Servers) and tick ‘DNS’.
3. Set up a DNS Profile on the virtual server
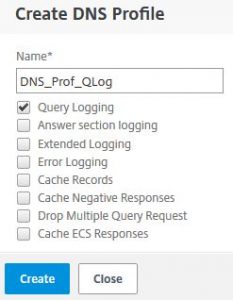
Now modify the DNS virtual server and add a DNS Profile to enable query logging. Go into your DNS virtual server, click the edit button under ‘Profiles’ and then click on the ‘Add’ button. Name your DNS profile and only tick ‘Query Logging’. Click on ‘Create’ and save the changes to the virtual server.
4. View captured traffic
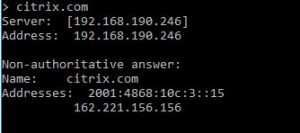
Generate some DNS traffic and view the logs in the NMAS syslog viewer (Networks / Events / Syslog Messages).
That is it and even though it might not be as ‘pretty’ as TCP/Security insight data, it will provide you with the information you need.
NOTE: The syslog viewer search function on NMAS seems a bit limited, as you can only ‘Search in the current page’. I’ve queried this with Citrix and the functionality enhancement is currently open under ENH0693183, with tentative delivery expected in Q3 2018.
UPDATE: This was fixed in version 12.0 Build 57.19.

Hi man, I’m struggling with the same issue.. search function in NMAS is really bad and indeed only searches in the current page. I configured the syslog for the appfw logging to see which signatures get hit
Oh yes, I have deployed the same build as you have :-). Did you ever get the search to function properly and / or search through all pages?
Thanks!
Ok me again. Just export to CSV and search through that. Except if you have found a better solution..
Glad to see I’m not the only one. No, I haven’t yet found a solution to this and I haven’t got any responses in Citrix discussions either.
Thanks, I’ll try the CSV export method, although it would be good if the syslog viewer worked properly!
Ok, even my export function is corrupt now. Can’t export to CSV anymore and export also seems limited to the first 50000 lines.
I ‘ve opened a discussion post here:
https://discussions.citrix.com/topic/393567-failed-to-export-the-report/